Use Case
Ransomware Recovery
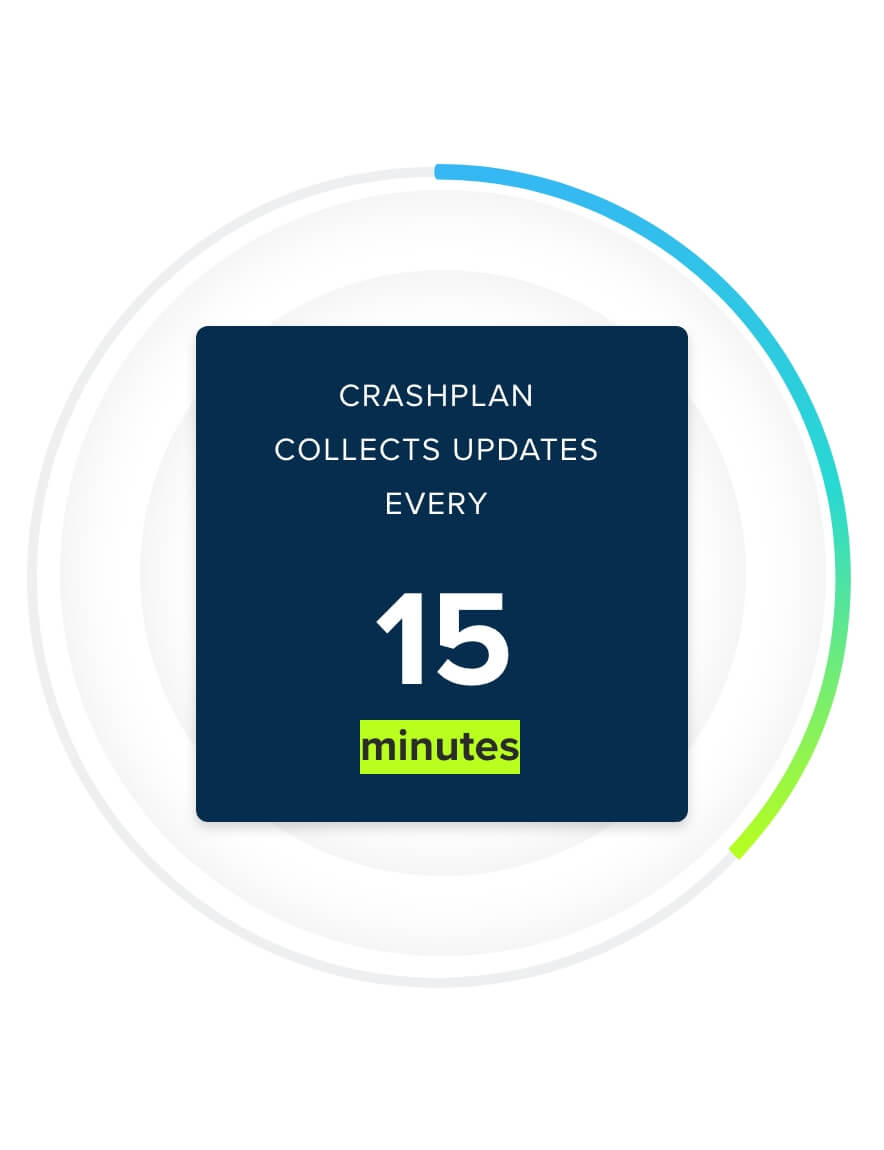
In 2023, over 70% of organizations hit with ransomware had their data encrypted, and the average recovery cost from ransomware attacks went up by 50%, according to a study from Sophos. CrashPlan helps you bounce back without extended downtime and without incentivizing cybercrime.